Privacy-focused crypto protocol Umbra said it has taken down its front-end website to make it more difficult for hackers who have been using it to move funds from recent “high-profile hacks.”
Umbra posted to X on Tuesday that it is aware that around $800,000 worth of stolen funds were moved via its protocol.
It added that it made the decision to move the hosted version of its front end into maintenance mode and would restore it “as soon as we are assured that doing so won’t create obstacles to the current recovery efforts.”
It comes just days after the Kelp protocol was exploited for over $280 million, which is suspected to have been carried out by North Korean hackers. Recent reports pointed to Umbra as among the protocols that the exploiter has been attempting to use to bridge funds from Ether to Bitcoin.
North Korean hacking groups are heavily sanctioned by the US, and multiple crypto platforms have worked to freeze or stifle the hackers’ efforts to move the funds.
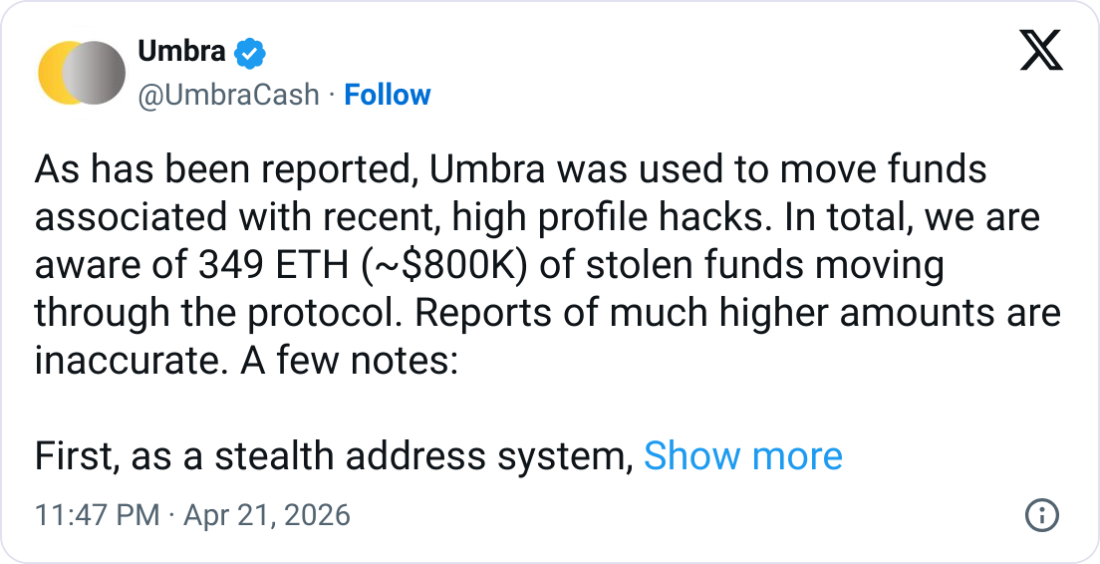
Umbra said, however, that there was “nothing we can do” to stop anyone from using its smart contracts or a local or self-hosted version of its open-source front end.
Roman Storm warns front end freeze isn’t enough
Roman Storm, co-founder of the crypto mixer Tornado Cash, argued the move to pause the front end may not be enough to avoid ire from authorities.
Storm was convicted in August of conspiring to operate an unlicensed money transmitting business, despite arguing that he was not in control of how the protocol was used.
“Prosecutors in my case called me a liar when I said that I can’t control Tornado Cash,” said Storm, who beat charges of conspiring to violate US sanctions.
He claimed that authorities viewed “changing a front end is the same thing as controlling an entire protocol.”
Related: Crypto hackers stole $17B over past 10 years: DefiLlama
“If you can make changes to the user interface, including further updates through new builds on IPFS, then you are in full control,” he added.
In its post, Umbra said that its protocol was “useful for protecting the identity of the receiver, not the sender,” and wasn’t useful for hackers wanting to obscure their money trail.
“All the stolen funds moved through the protocol can be identified, and we have been in touch with security researchers who are involved,” it added.
Magazine: South Korea gets rich from crypto… North Korea gets weapons
Go to Source to See Full Article
Author: Jesse Coghlan








